In this guide we will dump a memory partition from an Android device to do some forensic activities on it.
Prerequisites:
- Android rooted device
- A forensic workstation with adb (Android Dubug Bridge)
- busybox installed on the android device
First of all, we connect the Android device to our forensic workstation through USB, then we open a terminal.
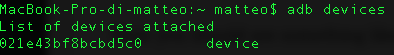
To ensure that the device is properly connected and ADB is working, we try to use this command:
$ adb devices
Then we should see something like this as output, that is the list of the connected devices:
Now that we are sure that the device is connected, we need to start an adb shell with this command:
$ adb shell
And then we become root with this command:
$ su -
Now we can list all the mounting points with their familiar names on the device with this other command:
# ls -al /dev/block/platform/msm_sdcc.1/by-name
** Please note that you need to check if on your device the directory name is msm_sdcc.1, if it isn’t please change with yours.
After we see all the mounting points with their familiar names (boot, cache, userdata…. ) something like the following output will appear.
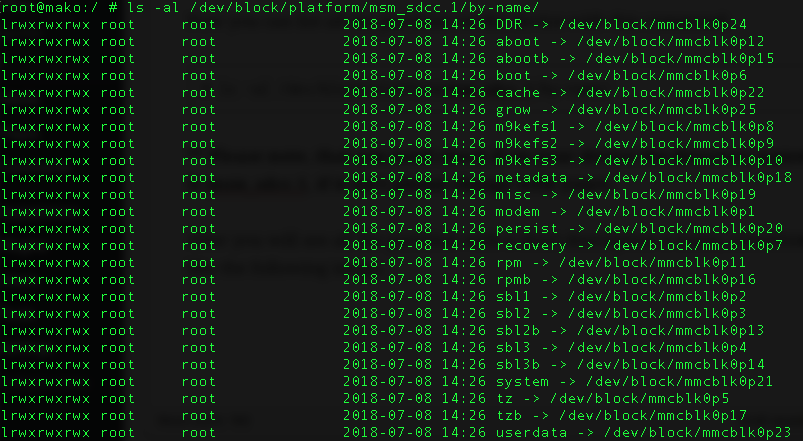
After this we can choose which of those blocks we want to dump, then we can use dd (data dump) command to create a bit-for-bit image. For transferring the file we use netcat.
First of all we open a new terminal screen, and we forward the port tcp 8888 as following: (Basically it means that the requests on port 8888 on the host will be forwarded to port 8888 on the device. Where the first port is the host and the second one is the device port)
$ adb forward tcp:8888 tcp:8888
Now we open an adb shell and become root as we did before:
$ adb shell $ su -
Now we start our data dumping and we append the output to an open port through busybox netcat (we will open the port 8888 for listening, the one that we enable to forwarding before), and we will receive the dump on another terminal:
# dd if=/dev/block/mmcblk0p23 | busybox nc -l -p 8888
Now immediately open on a new terminal on the forensics workstation with a netcat for retrieving the data:
$ nc 127.0.0.1 8888 > userdata_dump.img
When the dd finish, “userdata_dump.img” will be ready to be analyzed! Enjoy!
can i analyze this dump file with volatility?
Volatility is useful for volatile memory dump, I suggest you to use Autopsy, which is full of excellent android parsers.